How to Remove Stremanp.com Virus Redirect and POP-UP Ads
What is Stremanp.com
Stremanp.com is regarded as a very hazardous and awful hazard to the laptop that comes within the adware or browser hijacker category. It is also recognized as a potentially unwanted program that can get stealthy inside damaged PC to perform loads of malicious functions. In addition to this risk, it can connect to your operating browsers such as Chrome, Opera, UC, IE, Safari, Firefox, and many others.
Must visit: The PirateBay Proxy List For 2019 [100% Working Mirror Sites]
Stremanp.com is another online marketing campaign web address presently used by cyber perpetrators. When visiting suspect websites that run malicious advertising drive, web users are typically redirected to this website. Stremanp.com is an original pop-up website, accompanied by a sequence of redirects aimed at promoting a range of questionable apps and nameless websites.
Redirecting Internet browsers to Stremanp.com does not always indicate an outbreak with the virus. It is often provoked, as stated, by a script on harmful sites that have been visited. It suggested using these online shopping channels to obtain a very small and low-cost item. But the reality is that, by luring innocent users, it was created by a group of cybercriminals whose motivation is to gain earnings and income.
All such associated data is a PPC system, and once you press it, you will be redirected to a questionable malicious location where your system merges with other damaging viruses and threats. Therefore, if you want to maintain your system secure, you need to immediately cancel Stremanp.com.
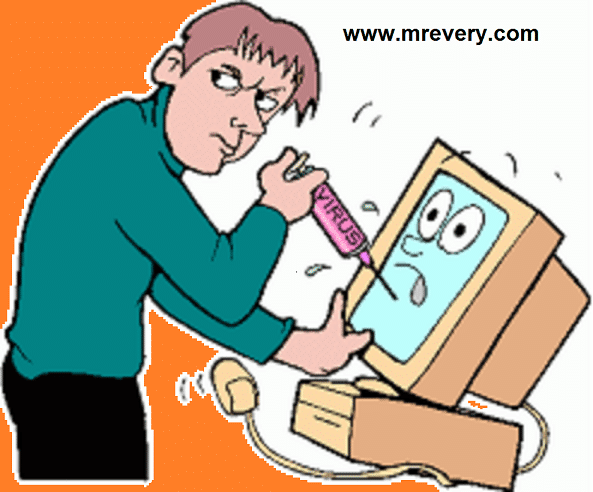
Why we have to secure our systems?
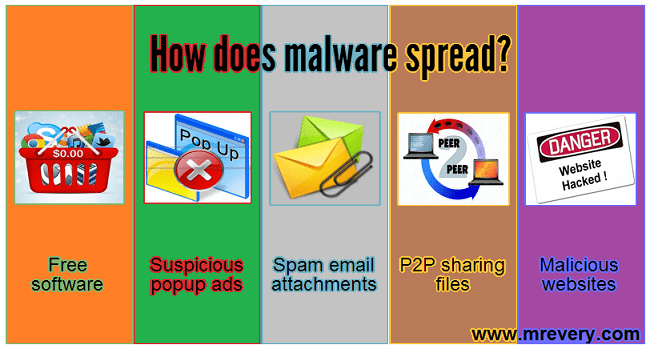
Ninety percent of the globe today is based on computer. So, why remain behind the criminals. Criminals are developing their own platform in this Internet globe to cheat customers. Not only this they developed loads of other viruses and malware rampantly, such as Stremanp.com is their creation. Research malware scientist found that millions of false programs, malicious codes, are published on a regular basis on the Internet. The only motivation for cybercriminals/hackers is to ruin your safety and obtain the information stored and misuse it in their illegal employment. That’s why you never want to learn how to safeguard your PC.
Read also: How to Sell on Pinterest: A Step-by-Step Guide for Grow Your Brand
10 Signs from which any users can get that their PC is infected by some Virus/malware like Stremanp.com
1. When ransomware hits your system, all your files are missing and some encrypted files are not more than 400 kb instead.
2. Whenever you use your default browser to browse something. An unwanted tab opens suddenly and gives you warning alerts “Your PC is infected with the need for immediate protection from [ 5 ] dangerous virus. Don’t believe the spam warning generated by virus or adware is on these alerts.
3. Sometimes you find that every time you start or crash your regular use of Application. This is because their DLL file is corrupted by malware and stops executing the application/program.
4. When it comes to your system, a browser hijacker virus is very annoying and hijacked your browser that you will not be able to surf the internet as you wish. It will always automatically open other tab or pages without your request. And sometimes some application you’ve found is downloaded automatically.
5. A computer is as strange as before; these are the main symptoms of malware for the registry editor. They add in the Windows Registry editor malicious registry entries that make it difficult to easily run OS [ Operating System ].
6. They use your internet to upload/download their malicious files on the internet that you may suffer from a slow internet connection or that you may not be able to connect to the internet.
7. It is also an indication of an infected system when automatically your some lawful application language has altered and your desktop wallpaper has altered from moment to moment.
8. Sometimes when a computer works strange like sending email to an unknown person without your knowledge and at booting executing an unknown program. These are the symptoms that a virus infects your computer that gives Cyber hackers full control of your computer.
9. Without your permission, some viruses like Trojan or ransomware can turn off your antivirus and Windows firewall. That’s why we recommend using an anti-malware program rather than an anti-virus program.
10. You also sometimes find that some of your regular program files are missing from the computer library. This happens when your local disk is hidden by a computer virus. It began to eat files and consume their resources
Read Also: Top 15 Kickass Torrent Mirror Sites and Pirate Proxy 2019 [100% Working Kickass Torrents]
How to remove Stremanp.com (Removal Procedure):
Method 1: Scan your computer with MBAM Tool
This extraction instrument for malware is free and simple to use. It searches, detects, and prevents threats such as trojan, virus, PUP, adware, and malicious redirects such as Stremanp.com. The instrument is sufficiently strong to discover dangerous objects concealed on the desktop.
Step 1: Download the free Malwarebytes Anti-Malware Scanner.
Please use the tool specifically intended for Macintosh users to remove Stremanp.com from Mac OS.
Step 2: Install the program after download. It may operate automatically or the downloaded file mb3-setup-consumer-x.x.x.xxxx.exe must be double-clicked.
Step 3: Use the default configuration to proceed with the installation. It is accessible on the download website if you need the full installation operation.
Step 4: Click Finish to operate the program at the last installation stage.
Step 5: Select Scan from the cabinet to see accessible Scan Method on the Malwarebytes Anti-Malware computer.
Step 6: Click Threat Scan next. This is the most extensive technique of scanning that is sure to discover any concealed objects related to Stremanp.com.
Step 7: To start inspecting the laptop, click the Start Scan key.
Step 8: Malwarebytes Anti-Malware will show the list of recognized risks when testing is completed. Remove all hazards recognized including Stremanp.com and restart the test method to complete the laptop.
Method 2: System Restore
Step 1: First users need to enter “System Properties” to generate System Restore Point and can search for “System Properties” straight from “START search panel” or unlock it via Windows Explorer by right-clicking on “my Computer.”
Step 2: You need to identify “System Protection” in left screen choices after opening “System Properties.” Just press the “System Protection” button and a fresh tab pops up.
Step 3: You will discover the button “System Restore” in “System Protection” just click on it and obey it as it says.
Step 4: It will tell you where and what title it should have to store the.img file “System Restore.” Just offer it an information storage route and a name.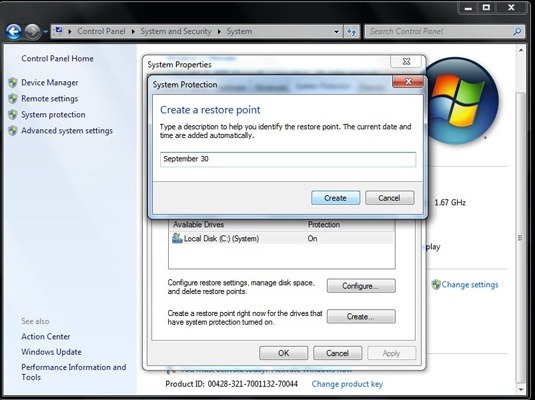
Step 5: It requires a little time to build a restore point (it’s just like a checkpoint you get while playing matches) and a pop-up arrives with a notification afterward.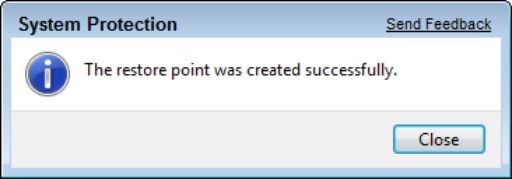
You’re talking about what to do with this now? Well people, I’d like to inform you that you’ve just developed a gun for yourself against viruses, malware, infections, errors, etc. because you’ve got a System Restore.img file, then whenever you think you’ve inserted some incorrect software or automatically placed it combined with some other implementation, you can use this “System Restore” to revert your system to the earlier phase you’ve developed. That implies all the problems that have passed away and you can begin from where you started.
Method 3: Automatic Removal Process
Automatic doesn’t mean that some wizard went to you reading some magical phrases and all the problems are gone. You must first enter the Anti-Malware program in this phase and then put it in “Safe mode.” There is a chance that Stremanp.com inside your PC will prevent you from running the program, so putting the program in “Safe Mode” is best. If you don’t know how to unlock “Safe Mode,” we’re going to inform you:
Step 1: Reboot your computer and press “F8″ continuously.
Step 2: You have options; here you have to select “Safe Networking Mode.” Your system began in “Safe Mode” and the program can now be installed.
Automatic removal process has a lot of advantages. Using the Anti-Malware Tool will save your time and deliver precise outcomes. Some malware has hidden files that are very difficult to remove manually, but anti-malware tools are very advanced and their databases are up to date so they will scan the entire system in a few minutes and remove every infected file from the computer.
Method 4: Stop Malicious Notifications and Ads from Browser
Ads from Stremanp.com may influence various browser programs. We, therefore, produced particular guidelines for different apps for internet software. These processes are covered by removing Stremanp.com advertisements from Google Chrome, Mozilla Firefox, and Microsoft Edge.
a) For Google Chrome
Step 1: Open the Google Chrome browser and type: chrome:/settings / content / notifications in the address bar area.
Step 2: Look for Stremanp.com in the Notifications section.
Step 3: Click More Actions … then Click Remove to stop pop-up ads on Stremanp.com.
Step 4: In the address bar type the following chrome://settings/cleanup
Step 5: Click Find button to locate and remove damaging Google Chrome apps and objects like Stremanp.com. Restart the scanning method when completed.
b) For Microsoft Edge
Step 1: Open the Microsoft Edge browser.
Step 2: On the top corner of the Edge window, click Settings and More.
Step 3: From the drop-down list, pick Settings.
Step 4: After that, Click on View Advanced Settings and under Website Permissions, click Manage.
Step 5: Now, from the list, discover Stremanp.com and cancel it or switch it off.
c) For Mozilla Firefox
Step 1: Open the Mozilla Firefox browser and type: about:preferences#privacy
Step 2: Navigate to Permissions section and click Settings in the Notifications area.
Step 3: Click the Remove Website button on Stremanp.com from the list.
Step 4: Now, Click Save Changes.
Step 5: In the address bar, type about: support
Step6: Click on Refresh Firefox button to restore the browser to clean state. and wait to finish the procedure until it restarts.
Method 5: Scan and Delete Adware with AdwCleaner
Steps to scan and delete adware with AdwCleaner are as follows-
Step 1: Download the AdwCleaner instrument from the place shown below.
Step 2: Please close all operating programs on the desktop once you have finished the download.
Step 3: To begin working the device, locate the folder and double-click ADW cleaner Ver.exe. Then press the Scan button.
Step 4: It checks for the existence of damaging programs, plug-ins, add-ons or any information that has been discovered to be malicious and connected to Stremanp.com.
Step 5: The tool may need to reboot your laptop once scanning is completed to finalize the cleaning method.
Step 6: AdwCleaner will show the latest test log file after rebooting.
READ ALSO:
- How To Delete and Temporarily Deactivate Your Kik Account
- Asus Zenfone 6 2019 (Zenfone 6z) Price in India June 2019, Specifications, Release Date
- Samsung Galaxy Note10 Pro Specification
- HR E-Mail Id’s
- Free Movies & TV Serials Download Sites For 2019
- How To Password Protect a Folder in Windows by cmd without any software
- Source Code for final year college student
- How to Download Video and Audio from YouTube for free





![How to Hack Facebook, Twitter, Gmail Using KeyLogger [Kali Linux – BeeLogger]](http://www.mrevery.com/wp-content/uploads/2020/06/How-to-Hack-Facebook-Twitter-Gmail-Using-KeyLogger-Kali-Linux-BeeLogger-800x450.jpg)